In an era where data privacy is a major concern, End-to-End Encryption (E2EE) has become a crucial technology to protect user communications from unauthorized access. At its core, E2EE relies on asymmetric encryption, which uses a pair of cryptographic keys—one public and one private—to ensure secure communication between parties. Because the Signal app has been in the news recently, this article explores how asymmetric encryption works in E2EE, how public and private keys function, and some of the most popular applications implementing this security measure.
Continue reading “End-to-End Encryption: A Secure Form of Asymmetric Encryption”LCDR Stephen R. Harris USN (Ret.)
March 31, 1938 – May 18, 2020
On March 28, 2025, Friday night, Jim Reeb passed away. His biography follows:
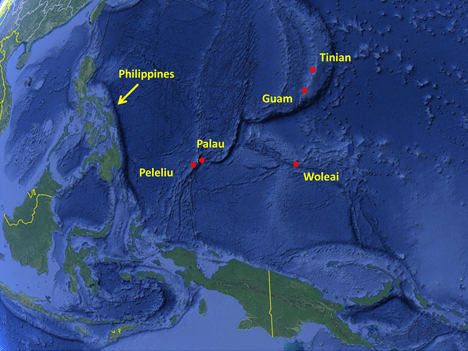
Continue reading “Honoring and Remembering James N. Reeb MCPO/CWO4) USN (Ret.)”Operation Desecrate One was a World War II United States Navy operation on 30–31 March 1944. Desecrate One was part of the preparations for Operations Reckless and Persecution, the Allied invasion of western New Guinea.
Continue reading “Operation Desecrate One Radio Intelligence After Action Report”The Millennium Challenge 2002 war game and the growing strategic challenge posed by China’s People’s Liberation Army Navy (PLAN) share critical similarities, particularly in how asymmetric tactics and adaptability can counter the technological and numerical superiority of the U.S. military. Both scenarios reveal the potential vulnerabilities of a U.S. force that relies heavily on centralized command structures, advanced sensor networks, and electronic warfare capabilities, only to be outmaneuvered by a more flexible and unconventional adversary.
Continue reading “Millennium Challenge 2002 and the Strategic Lessons for a Conflict with the Chinese PLAN”